Welcome to our article on spillage prevention measures, spill prevention techniques, and spillage prevention strategies for 2024. In the Cyber Awareness Challenge 2024, it is crucial to influence user behavior and ensure the security of DoD Information Systems. One key aspect of this training is preventing spillage, which involves protecting classified or sensitive information from unauthorized access or transfer.
To effectively prevent spillage, it is important to follow procedures for transferring data to and from outside agencies. Additionally, it is vital not to assume that open storage is authorized for classified information and to proactively identify potential insider threats. By implementing these good practices, you can play an active role in mitigating threats and vulnerabilities to information security.
Join us as we dive into the importance of information safeguarding, spillage prevention techniques and guidelines, securing information on removable media and mobile devices, best practices for social networking and website use, safeguarding classified and sensitive information, insider threat prevention and management, and telework and home computer security. Let’s explore how you can contribute to an effective spillage prevention strategy in 2024.
Importance of Information Safeguarding
Safeguarding information is crucial to prevent spillage. Unauthorized access to classified or sensitive information can lead to serious consequences. It is important to follow established procedures for transferring data, handle classified information with care, and identify and report any suspicious or unauthorized activities. Implementing best practices for spillage prevention, such as storing classified information in locked drawers and proactively identifying and addressing insider threats, can significantly reduce the risk of spillage.
Best Practices for Spillage Prevention
- Follow established procedures for transferring data to ensure it is shared securely.
- Handle classified information with utmost care, ensuring it is protected at all times.
- Identify and report any suspicious or unauthorized activities immediately.
- Store classified information in locked drawers or safes when not in use.
- Proactively identify and address insider threats within the organization.
By implementing these best practices, individuals and organizations can effectively prevent spills and protect sensitive information from unauthorized access.
“Proper information safeguarding is essential to prevent spillage and protect sensitive data from falling into the wrong hands.” – Security Expert
| Spillage Prevention Best Practices | Benefits |
|---|---|
| Follow established procedures | Ensures secure data transfer |
| Handle classified information with care | Prevents unauthorized access |
| Report suspicious activities | Allows for timely action |
| Store classified information securely | Reduces risk of unauthorized disclosure |
| Proactively address insider threats | Enhances overall security posture |
Implementing these spillage prevention best practices is essential for maintaining the confidentiality and integrity of sensitive information.
Spillage Prevention Techniques and Guidelines
To effectively prevent spillage, organizations and individuals should adhere to specific techniques and guidelines. By following these spillage prevention methods, one can significantly reduce the risk of unauthorized disclosure of sensitive information. Spillage prevention guidelines encompass a range of measures, from securing digital communication to safeguarding physical spaces.
Guideline 1: Ensuring Proper Clearance and Need-to-Know
Before transmitting Controlled Unclassified Information (CUI) via encrypted email, it is essential to verify that all recipients have the necessary clearance and need-to-know. This helps prevent spillage and ensures that sensitive information is shared only with authorized individuals.
Guideline 2: Avoiding Social Media Pitfalls
Posting sensitive information on social networking sites poses a significant risk. Adversaries can exploit these platforms to disseminate fake news or gain unauthorized access to confidential data. To prevent spillage, it is best to exercise caution and refrain from sharing any sensitive or classified information on social media.
Guideline 3: Implementing Physical Security Measures
Good physical security practices play a crucial role in spillage prevention. Challenging individuals without proper identification and taking proactive steps to prevent unauthorized access to classified spaces can help mitigate the risk of spillage. By implementing robust physical security measures, organizations can safeguard their sensitive information effectively.
“The proper implementation of spillage prevention guidelines ensures that sensitive information remains confidential and protected from unauthorized access.”
By adhering to these spill prevention tips and guidelines, organizations and individuals can proactively mitigate the risks associated with unauthorized disclosure. Implementing effective spillage prevention methods goes a long way in safeguarding sensitive information and maintaining the integrity of classified data.
Securing Information on Removable Media and Mobile Devices
Properly securing information on removable media and mobile devices is essential for effective spillage prevention. By implementing the spill control practices outlined below, individuals and organizations can significantly reduce the risk of unauthorized information disclosure.
-
Storage of Government-Owned Removable Media
Storing government-owned removable media in GSA-approved containers based on the appropriate security classification helps minimize the potential for spillage. These containers provide an added layer of physical protection for sensitive information, reducing the risk of unauthorized access or accidental loss.
Protecting Data on Mobile Devices
Ensuring the security of data on mobile devices is crucial for spillage prevention. By following these spillage prevention solutions, individuals can safeguard their information:
- Enable automatic screen locking: Configure devices to automatically lock after a specified period of inactivity. This helps prevent unauthorized access to the device and the information stored within.
- Use strong and unique passwords: Set a strong password or passcode on the device, making sure it is not easily guessable. Avoid using common passwords or personal information that could be easily associated with you.
- Exercise caution when downloading and installing applications: Stay vigilant when downloading apps, and only download from trusted sources such as official app stores. Be mindful of the permissions requested by applications and ensure they align with their intended functionality.
-
Regularly Update Devices and Use Encryption Technologies
Keeping devices up to date with the latest security patches is crucial for minimizing vulnerabilities that could be exploited by threat actors. Additionally, enabling encryption technologies, such as device encryption or encrypted communication channels, enhances the protection of sensitive information stored on mobile devices.
By adhering to these spillage management strategies, individuals and organizations can create a strong defense against information spillage and maintain the confidentiality of their sensitive data.
| Spillage Prevention Solutions | Spillage Control Practices | Spillage Management Strategies |
|---|---|---|
| Storage of Government-Owned Removable Media | Enable Automatic Screen Locking | Regularly Update Devices and Use Encryption Technologies |
| Protecting Data on Mobile Devices | Use Strong and Unique Passwords | |
| Exercise Caution when Downloading and Installing Applications |
Social Networking and Website Use Best Practices
When it comes to information security, social networking and website use can pose significant risks if not managed properly. It’s crucial to exercise caution and follow best practices to prevent spills and protect sensitive information. By implementing effective spillage prevention techniques, you can mitigate the potential risks associated with these platforms.
Best Practices for Preventing Spills
- Avoid posting identifiable landmarks in photos: Adversaries can use these landmarks to gather information about your location and potentially exploit it.
- Research the credibility and reliability of websites: Before providing any personal or sensitive information, ensure that the website is trustworthy and legitimate.
- Avoid clicking on suspicious links or downloading files from unknown sources: These could contain malware or lead to phishing attempts.
It’s important to be mindful of the potential for adversaries to exploit social networking sites for malicious purposes. By following best practices, you can minimize the risk of spills and protect your personal and sensitive information from unauthorized access.
Spillage prevention methods such as these are essential for maintaining information security and protecting sensitive data. By prioritizing best practices, you can reduce the likelihood of spills and safeguard your digital presence.
| Best Practices | Benefits |
|---|---|
| Avoid posting identifiable landmarks in photos | Prevents adversaries from gathering information about your location. |
| Research credibility and reliability of websites | Ensures that you provide personal or sensitive information only to trustworthy sources. |
| Avoid clicking on suspicious links or downloading files from unknown sources | Minimizes the risk of malware infections and phishing attempts. |
By regularly practicing these spill prevention techniques, you can maintain a strong defense against potential threats and protect your information from unauthorized access.
Safeguarding Classified and Sensitive Information
Safeguarding classified and sensitive information is crucial to prevent spills and ensure the security of data. Effective spill prevention methods involve following strict protocols and implementing best practices for handling sensitive documents.
One of the key practices is to ensure that open storage of classified information is not assumed to be authorized. It is essential to establish procedures that clearly define the proper storage and handling of sensitive documents, reducing the risk of unauthorized access and potential spillage.
In addition, it is important to handle physical documents with care and take necessary precautions to protect them from accidental access or unauthorized retrieval. This includes storing them in secure containers, locking drawers, or using other appropriate storage measures.
Reporting any incidents of suspicious or unauthorized access is also crucial in preventing spills. By promptly reporting such incidents, organizations can take immediate action to prevent further compromise of sensitive information. Encouraging a culture of vigilance and empowering employees to report potential security breaches is essential for maintaining information security.
Physical security measures play a vital role in spill prevention. Controlling access to secure areas and verifying the identification of individuals help safeguard classified information from unauthorized disclosure. By implementing these practices, organizations can maintain tighter control over access to sensitive areas and reduce the risk of spills through unauthorized physical access.
Another important aspect of spill prevention is applying dissemination controls to Controlled Unclassified Information (CUI). These controls ensure that only authorized individuals have access to the information and prevent unauthorized sharing or distribution. By carefully managing the dissemination of CUI, organizations can minimize the risk of spills and maintain the confidentiality of sensitive data.
Best Practices for Preventing Spills:
- Establish clear storage and handling protocols for classified information
- Handle physical documents with care and store them in secure containers or locked drawers
- Promptly report any incidents of suspicious or unauthorized access to sensitive information
- Implement physical security measures, such as controlling access to secure areas
- Apply dissemination controls to Controlled Unclassified Information (CUI)
By following these spill containment practices and implementing the best practices for preventing spills, organizations can significantly reduce the risk of unauthorized disclosure of classified and sensitive information.
| Spill Prevention Methods | Spill Containment Practices | Best Practices for Preventing Spills |
|---|---|---|
| Establish clear storage and handling protocols | Store physical documents in secure containers | Promptly report incidents of unauthorized access |
| Implement physical security measures | Control access to secure areas | Apply dissemination controls to CUI |
Cyber awareness challenge 2023 2024 knowledge check
In navigating the ever-evolving landscape of cybersecurity, the Cyber Awareness Challenge 2024 stands as a beacon of knowledge and preparedness. As we embark on this educational journey, it’s imperative to arm ourselves with the tools and knowledge to combat potential threats. Let’s dive into an in-depth exploration of cybersecurity best practices and guidelines to safeguard sensitive and classified information effectively.
Cyber Awareness Challenge 2023 2024 Knowledge Check
The Importance of Following Established Procedures
One fundamental aspect highlighted in the DoD Cyber Awareness Challenge is the necessity of adhering to established procedures for data transfer. Such procedures ensure the secure sharing of information, thus playing a pivotal role in preventing unauthorized access or spillage. It’s crucial to remember that the correctness of our actions in handling data directly influences our collective security.
Safeguarding Classified Information: A Core Practice
To protect classified information, a comprehensive understanding of security best practices is essential. Among these practices, ensuring the absence of open storage for classified data and seeking proper authorization before removing sensitive information are paramount. Each action we take must be measured and deliberate, aimed at fortifying the barriers against potential breaches.
Insider Threat Awareness: A Reportable Concern
The challenge also stresses the importance of recognizing and addressing insider threats. Any instance where a colleague removes sensitive information without seeking proper authorization constitutes a reportable insider threat. Vigilance and prompt reporting of such activities are critical in maintaining a secure information environment.
Enhancing Physical and Digital Security Measures
Physical security measures, such as ensuring no identifiable landmarks are visible during virtual meetings and secure storage of removable media, are vital. Digital vigilance, including the cautious handling of emails with classified attachments and the appropriate marking of all classified materials, reinforces our defense against unauthorized disclosures.
Engaging in Cyber Protection
Understanding the various levels of damage that unauthorized disclosure could inflict upon national security is a core component of cyber awareness. The challenge prepares us to prioritize focus on critical information, ensuring that our actions do not inadvertently lead to serious damage to national security.
Effective Communication and Handling of Information
When faced with inquiries from external parties, such as reporters, the challenge guides us to neither confirm nor deny information that hasn’t been cleared for public release. This cautious approach to communication prevents the unintentional spillage of potentially classified information.
Mastery of Cyber Awareness Challenge Knowledge Check
To excel in the Cyber Awareness Challenge 2024 Knowledge Check, one must internalize these principles, understanding that each practice, from safeguarding information to recognizing insider threats, contributes to a robust cybersecurity posture. The challenge isn’t merely about correct answers but about ingraining a culture of security awareness that extends beyond the confines of the challenge.
Final Thoughts
The Cyber Awareness Challenge 2024 serves not only as a knowledge check but as a comprehensive guide to responsible information handling in an increasingly digital world. By internalizing these practices, we ensure that our actions consistently reflect a commitment to safeguarding national security and protecting sensitive information. As we progress through the challenge and beyond, let’s carry forward the lessons learned, maintaining a vigilant stance against potential cyber threats.
Expert-Verified Answerquestion
In today’s digital age, understanding the complexities of cybersecurity and spillage prevention is crucial. The Cyber Awareness Challenge 2023-2024 is designed to arm individuals with the knowledge to protect classified and sensitive information effectively. Let’s delve into some of the core principles and expert-verified answers to frequently asked questions and scenarios you might encounter.
Understanding the Basics: What is True?
One of the foundational truths in cybersecurity is that not all storage is authorized for classified information. This underlines the importance of adhering to established protocols for data handling and storage, ensuring that sensitive information remains secure and out of reach from unauthorized access.
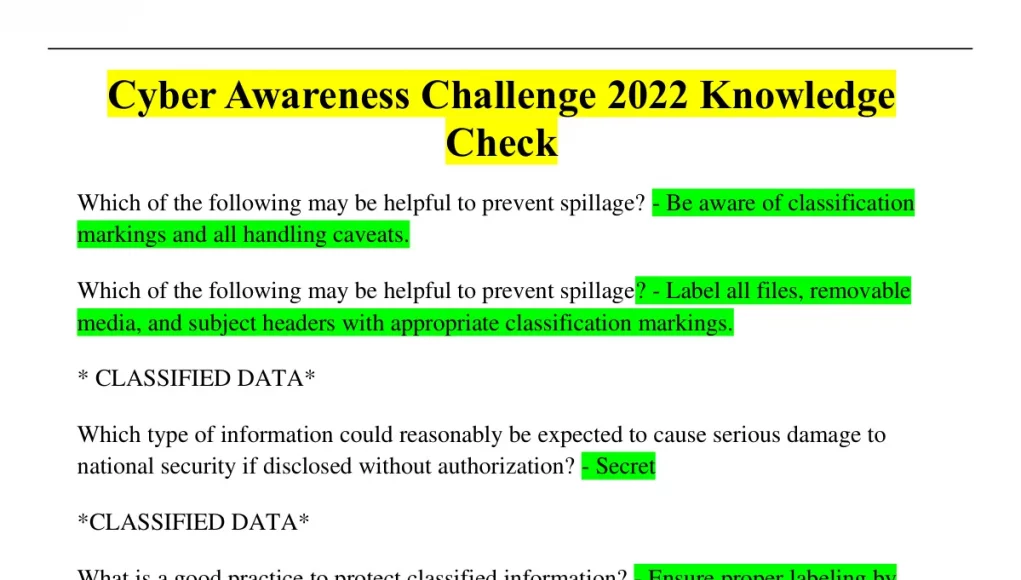
Preventing Spillage: What May Help?
To prevent spillage, following established procedures for transferring data is paramount. This includes verifying the clearance of recipients before sharing Controlled Unclassified Information (CUI) and encrypting emails to protect the integrity of the information being shared.
Good Practices to Protect Classified Information
A security best practice for protecting classified information is to store it in locked drawers or safes when not in use. This physical security measure minimizes the risk of unauthorized disclosure and is a fundamental step in safeguarding sensitive data.
Security in Communication: What is Expected?
When receiving an inquiry from a reporter or any external party about sensitive projects, the expected response is to neither confirm nor deny the information unless it has been cleared for public release. This practice helps in avoiding inadvertent spillage of potentially classified information.
Insider Threat Awareness: What is Reportable?
A reportable insider threat scenario could involve a colleague removing sensitive information without seeking proper authorization. Recognizing and reporting such actions promptly is critical in mitigating risks and protecting against potential insider threats.
On Visibility and Discretion
Ensuring there are no identifiable landmarks visible during virtual meetings or in photographs shared on social media is a good practice. This helps prevent adversaries from gathering information about your location or the project’s specifics, thereby safeguarding sensitive data.
Cyber Awareness Knowledge Checks
- Dod Cyber Awareness Challenge Knowledge: It emphasizes the importance of continuous learning and staying updated with cybersecurity practices to defend against evolving threats.
- Awareness Challenge Knowledge Check 2023: This challenge serves as a reminder that cybersecurity is not just about technology but also about understanding human behavior and potential insider threats.
Essential Measures for Security
- Cyber Protection Condition: Understanding and adhering to the current cyber protection condition (CPCON) levels can help in adjusting security measures according to the threat landscape.
- Sensitive Compartmented Information Facility (SCIF): Working within a SCIF requires strict adherence to protocols designed to prevent unauthorized access to sensitive information.
Conclusion
The Cyber Awareness Challenge 2023-2024 reinforces the critical role of vigilance, proper handling, and the secure sharing of information in maintaining national security and protecting sensitive data. By following these expert-verified answers and incorporating these practices into our daily operations, we contribute to a stronger, more secure digital environment.
What does this mean?
Navigating Cybersecurity: Understanding the Core of Cyber Awareness
In the realm of Cyber Awareness Challenge 2023-2024, our digital ecosystem is akin to a vast ocean, teeming with potential threats lurking beneath its surface, waiting to breach the security of our ships – our sensitive and classified information. Let’s embark on a voyage to demystify the principles of cybersecurity, steering through the waters with knowledge and vigilance as our compass.
What Does “Following is True” Mean?
In the cybersecurity realm, acknowledging what is true is akin to recognizing the North Star in a sailor’s journey. It guides us in understanding that open storage is not authorized for classified information, a principle that serves as a beacon for securing sensitive data.
How Can We Prevent Spillage?
Preventing spillage is like ensuring our vessel is watertight. By following established procedures for data transfer and ensuring no identifiable landmarks are visible in shared images, we create an impermeable barrier against the sea of threats. These actions are buoys that mark the safe passage through dangerous waters.
The Security Best Practices Compass
Adhering to security best practices is our compass, guiding us through foggy seas. Storing classified information securely and being cautious of sharing sensitive data on social media are the cardinal points that keep our journey on the right path. Just as a ship’s captain reviews their compass regularly, we must continuously reassess our cybersecurity practices.
The Lighthouse: Insider Threat Prevention
Recognizing a reportable insider threat is like spotting a lighthouse warning us of danger ahead. Whether it’s a colleague removing sensitive information without authorization or a vendor conducting a pilot program without the proper clearance, these are signals that require immediate attention. Like a lighthouse, they alert us to take corrective action to avoid a potential shipwreck.
Cyber Awareness 2022-2023: The Charted Map
Our journey through cyber awareness is guided by a map charted through experiences and lessons learned. The Cyber Awareness Challenge 2022 laid down the coordinates for navigating the digital seas, emphasizing the significance of marking classified material appropriately and the priority focus on critical information. Each point on this map is a milestone in our ongoing quest to bolster our defenses.
The Anchor: Spillage Refer and Information Security
Understanding spillage and its implications anchors our ship, preventing it from drifting into hazardous territories. Whether it’s through encrypting emails with classified attachments or implementing strict access controls to classified systems, these measures are the anchor that keeps our ship safe in harbor.
Setting Sail with Knowledge
As we set sail in the vast ocean of cyber awareness, let us remember that the principles of cybersecurity are our compass, map, anchor, and lighthouse. They guide us, warn us of dangers, stabilize our journey, and illuminate our path. With this knowledge, we can navigate the seas confidently, ensuring the safety of our digital assets against the ever-present threats.
Embarking on this voyage with the Cyber Awareness Challenge 2023-2024, we are not just passengers but active participants in securing our digital realm. Let’s hoist our sails with wisdom and vigilance, for in the world of cybersecurity, our collective efforts keep the waters safe for all.
Which of the following is a good practice to prevent spillage 2023 cyber awareness?
Which of the Following is a Good Practice to Prevent Spillage 2024 Cyber Awareness?
Embracing the Culture of Security Awareness
As we stand on the cusp of 2024, one fundamental truth remains unchanged: knowledge is power. In the realm of cyber security, this adage manifests through continuous education and awareness. The cyber awareness challenges of 2023 have laid the groundwork, emphasizing the need for vigilance and informed action. Regular training sessions and knowledge checks, akin to the ones seen in the cyber awareness challenge 2022, serve as the cornerstone for developing a robust security posture. These initiatives enlighten individuals on the “do’s and don’ts,” equipping them with the knowledge to identify and avert potential security breaches.
Rigorous Access Controls: The Gatekeepers of Information
In the digital fortress that safeguards our sensitive data, access controls act as the discerning gatekeepers, determining who may enter and who shall not pass. Ensuring proper clearance and adhering to the principle of least privilege are not mere suggestions but mandatory practices. Just as a castle’s gates remain closed to all but those with explicit permission to enter, so too must our data be inaccessible to anyone lacking the requisite clearance and need-to-know basis. This selective access is pivotal in preventing unauthorized spillage, thereby preserving the sanctity of our classified information.
The Digital Footprint: Navigating the Social Media Maze
The allure of social networking sites is undeniable, yet within this digital maze lies the potential for spillage. Discerning navigation through this maze requires a cautious approach, reminiscent of a sailor steering clear of treacherous waters. Sharing sensitive information on such platforms is akin to casting a message in a bottle into the vast ocean, where it may reach unintended shores. Hence, the golden rule: refrain from posting or discussing any information that could compromise our security. This restraint is a testament to our commitment to prevent spillage and protect national security.
The Shield of Encryption: Guarding Our Digital Realms
In our battle against spillage, encryption stands as a formidable shield, cloaking our data in a layer of secrecy that is penetrable only by those with the key. Encrypting emails containing Controlled Unclassified Information (CUI) and using encrypted channels for communication are practices not just recommended but required. Imagine encryption as the arcane spell that renders a treasure invisible, accessible only to those who know the magic words. This magical shield is our best defense, ensuring that our secrets remain just that—secret.
Insider Threats: The Enemy Within
Among the myriad challenges we face, the threat from within looms large. The potential insider, motivated by malice or mishap, presents a risk that is as real as it is challenging to mitigate. Recognizing the signs—many potential insider threat indicators—demands a keen eye and a proactive stance. Establishing insider threat programs and fostering an environment where suspicious behavior is promptly reported are not mere strategies but necessities. It’s akin to having sentinels within our walls, ever-watchful for signs of betrayal.
As we march forward into 2024, armed with the lessons of the past and the resolve to secure our digital future, let us remember that preventing spillage is not the responsibility of the few but the duty of all. The practices outlined herein are not just guidelines but pillars upon which the security of our information stands. Together, as custodians of data in this digital age, we hold the key to safeguarding our future against the ever-evolving threats that lie in wait.
Which of the following statements is true cyber awareness 2023?
In our quest to fortify our digital ramparts against the incessant tide of cyber threats, it becomes imperative to shine a beacon on the principles and strategies that will guide us through the murky waters of information security. As we set our sights on the Cyber Awareness Challenge 2024, let us unravel the tapestry of measures and tactics that constitute the bedrock of spillage prevention. With the compass of our collective knowledge, we shall navigate the complex seas of safeguarding sensitive information, ensuring that our voyage towards a secure digital future is both steadfast and unerring.
Which of the Following Statements is True: Cyber Awareness 2023?
The Shield of Vigilance: Preventing Unauthorized Access
In the realm of digital fortitude, the axiom “forewarned is forearmed” holds unparalleled significance. The tenet that underpins our security apparatus is the unwavering vigilance against the unauthorized access of sensitive data. This foundational principle mandates the meticulous vetting of access privileges, ensuring that only those with a legitimate need-to-know are granted the keys to the kingdom. Such a practice is not merely a security best measure; it is the bulwark that guards against the inadvertent breach of our digital sanctum.
The Map of Diligence: Insider Threats and Their Indicators
Embarking on this voyage, we acknowledge that the specter of insider threats looms as a formidable adversary. The recognition of potential insider threat indicators serves as our map through treacherous waters, guiding us in identifying those within our ranks who might, wittingly or unwittingly, jeopardize the sanctity of our information. It is a truth universally acknowledged in cyber awareness 2023 that a vigilant organization, alert to the signs of potential betrayal, is well-equipped to navigate away from the shoals of compromise.
The Beacon of Prudence: Handling and Storing Classified Information
As custodians of information that, if disclosed without authorization, could compromise national security, we are entrusted with a grave responsibility. The principles of appropriately marking all classified material and ensuring its storage on designated classified systems are not merely procedural formalities but sacred duties. Each document, each byte of data, when moved or shared, must be handled with the utmost care, shepherded securely within the confines of authorized channels. This diligence prevents spillage, safeguarding our collective security.
The Compass of Accountability: Reporting and Preventing Spillage
In the unending quest to preserve the integrity of sensitive data, the act of reporting unauthorized disclosures embodies the spirit of accountability. Whether it’s an email with a classified attachment sent in error or sensitive information glimpsed on an unsecured screen, the prompt reporting of such incidents is a clarion call to action. This practice, deeply ingrained in the ethos of cyber awareness 2023, is a testament to the collective responsibility we bear in the defense of our digital domain.
As we cast our gaze towards the horizon, let us embrace these truths with unwavering resolve. The journey through the digital age is fraught with challenges, yet armed with the knowledge and practices espoused in Cyber Awareness 2023, we stand ready to confront these perils. Together, vigilant, diligent, prudent, and accountable, we forge ahead, steadfast in our commitment to safeguard our information and secure our future.
Insider Threat Prevention and Management
Insider threats can pose a significant risk to information security and effective spillage prevention strategies. To mitigate this risk, organizations should establish Insider Threat Programs. These programs proactively identify potential threats and formulate spill control measures to prevent unauthorized access to sensitive information.
One of the key spillage prevention tactics is training individuals to recognize and report suspicious behavior. By educating employees about the risks associated with attempting to access sensitive information without authorization, organizations can create a culture of awareness and vigilance.
It is also crucial to establish clear procedures for reporting insider threat activity. This ensures that any potential breaches are promptly addressed, investigated, and resolved. By having a well-defined reporting process in place, organizations can minimize the impact of insider threats and prevent spillages.
| Insider Threat Prevention and Management Strategies: |
|---|
| Create an Insider Threat Program dedicated to spillage prevention. |
| Train employees to recognize and report suspicious behavior. |
| Establish clear procedures for reporting insider threat activity. |
| Ensure appropriate personnel are alerted in case of potential breaches. |
By implementing effective spillage prevention strategies and emphasizing the importance of insider threat management, organizations can protect their sensitive information and prevent spillages from occurring.
Telework and Home Computer Security
With the increasing trend of telework, it is essential to prioritize spillage prevention in the context of remote work. By implementing effective practices, individuals can ensure the security of sensitive information and maintain confidentiality. Here are some spillage prevention techniques and best practices for telework and home computer security:
1. Position Monitors Strategically
When working remotely, it is crucial to position monitors so they are not facing others. This prevents unintended exposure of sensitive information to unauthorized individuals. By being mindful of the monitor’s placement, you can ensure that confidential data remains confidential.
2. Obtain Proper Authorization
Never take sensitive information home without proper authorization. It is vital to follow established procedures and guidelines when it comes to accessing and handling classified or sensitive data outside of a secure office environment. By obtaining the necessary permissions and approvals, you can help prevent spillage.
3. Strengthen Home Computer Security
The security of your home computer plays a significant role in spillage prevention. To protect sensitive information, follow these best practices:
- Use strong and unique passwords for your devices and online accounts
- Enable automatic screen locking to prevent unauthorized access
- Regularly update software and security patches to keep your system protected
By taking these simple but effective steps, you can significantly enhance the security of your home computer and minimize the risk of spillage.
“Spillage prevention is not an option; it is a responsibility. Just as we secure our physical work environment, we must also prioritize the security of our home offices to prevent spills and protect sensitive information.”
4. Educate and Promote Awareness
Education and awareness are essential components of spillage prevention. Remote workers should be educated about the potential risks and consequences of spillage. Regular training sessions and awareness campaigns can help reinforce best practices and instill a culture of security.
5. Maintain Communication Channels
While working remotely, it is crucial to maintain open communication channels with your organization’s IT support team or security personnel. If you encounter any suspicious activity or believe that spillage may have occurred, report it immediately to the appropriate authorities. Prompt reporting can help mitigate the impact of a spillage incident.
Implementing these spillage prevention techniques and following the best practices for telework and home computer security can significantly reduce the risk of unauthorized information disclosure and help maintain the confidentiality of classified or sensitive data.
| Spillage Prevention Techniques | Benefits |
|---|---|
| Strategic placement of monitors | Minimizes unauthorized access to sensitive information |
| Obtaining proper authorization | Prevents unauthorized handling of classified data |
| Strengthening home computer security | Enhances the overall security of sensitive information |
| Educating and promoting awareness | Instills a culture of security and vigilance |
| Maintaining communication channels | Facilitates prompt reporting and incident response |
Spillage prevention is a critical aspect of information security in 2024. By implementing the best practices and following established guidelines, individuals and organizations can effectively reduce the risk of spills and protect sensitive information.
Securing information on removable media and mobile devices is key to preventing spills. Storing government-owned removable media in GSA-approved containers and using encryption technologies can help mitigate the risk. Practicing caution on social networking sites and websites is also crucial. Being mindful of what information is shared online and avoiding clicking on suspicious links or downloading files from unknown sources are essential spillage prevention techniques.
Furthermore, safeguarding classified and sensitive information is vital. Taking precautions such as not assuming open storage is authorized for classified information, handling physical documents with care, and reporting any suspicious or unauthorized access contribute to effective spill prevention.
Lastly, promoting awareness of telework and home computer security is important in the era of remote work. Following spillage prevention strategies like positioning monitors properly during telework and securing home computers with strong passwords and regular software updates contribute to overall spillage prevention in 2024.